Last week I passed the latest version of the AWS Security Speciality (SCS-C02). The Security Speciality certification assesses your knowledge of the various AWS security services, and the security capabilities of more general services offered by AWS. Big shoutout to the AWS Community Builders ! One of the perks of the program is a free AWS certification exam voucher, which I used to take this exam.
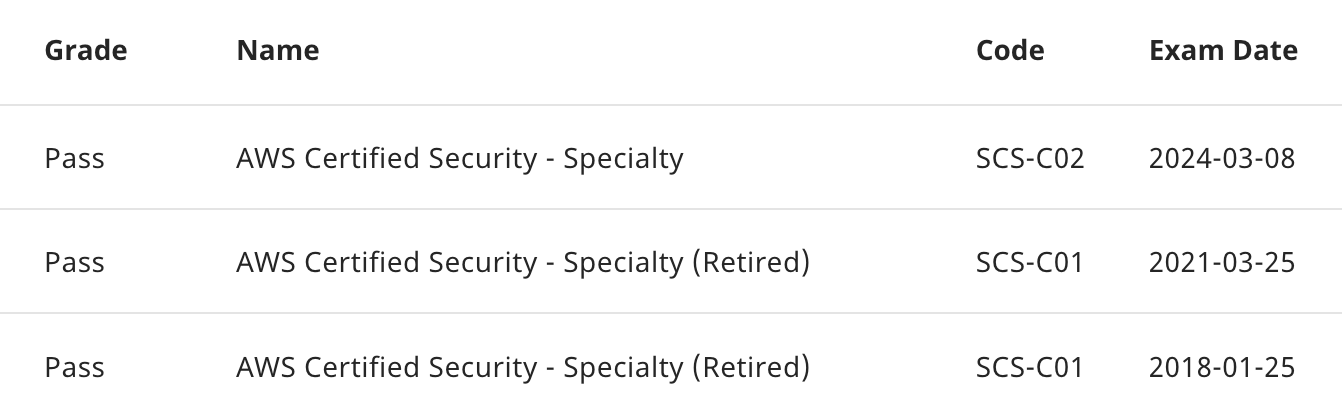
I really like this exam, and have been taking it since it was announced in beta back in early 2018:
It helps that I like AWS IAM more than most, and IAM is a big part of the exam. That being said, I think the new version of the exam (released in 2023) is a really good update that gives it more breadth, while still focusing on the most relevant security-related services in AWS - it helps that there are so many of them now!
If you want to pass the Security Speciality, you need know the official exam guide (PDF) intimately. All the exam questions are written with the guide in mind, so you can't be too familiar with it.
Here are the high level observations from my experience with the exam, keeping in mind that the questions are pulled from a large pool and are continually updated (I know because I wrote a few of them), so your milage may vary!
Exam Impressions
For all questions, even for other AWS certification exams, keep in mind the following:
- Focus on the specific services mentioned in the question, as this will help you eliminate some of the distractor responses. Look specifically for services not mentioned by function rather than name, for example "global cache" is CloudFront, "object storage" is S3, "threat detection" is GuardDuty, etc.
- Be clear what the priority is: the common ones are operational overhead or cost efficiency, which will enable to you pick between two similar responses. In most cases, a question that asks "least operation overhead" generally wants you to pick the response(s) with more AWS services.
Specific Examples
Systems Manager Parameter Store (specifically Secure String parameters) is often positioned as a cheaper (aka. "cost-effective") option to AWS Secrets Manager. Just remember that only Secrets Manager can automatically rotate secrets, so some solutions will require it, regardless of cost.
Know the differences between AWS KMS and AWS CloudHSM. This is particularly relevant when deleting keys: KMS has a mandatory waiting period, but CloudHSM can delete keys immediately. KMS also supports different types of key material, and there are limits to when you can/can't use them which you should know. Spend some time understanding KMS key grants - they are like resource policies for KMS keys, and will definitely feature in your exam.
IAM policy syntax and evaluation is a must! You will have multiple questions in this exam that will require you to read, understand, and choose between different policies. Of course if you need help with that, I got you 😉
This also includes SCPs, which are technically part of AWS Organizations but follow the same policy syntax as IAM. You should also know some of the common AWS IAM Conditions like those for checking MFA is present, etc. I had a couple of questions which required NotAction, which can be counterintuitive, but required to achieve some scenarios.
Know the difference between gateway endpoints and interface endpoints for VPCs. Gateway endpoints are an older (pre-PrivateLink approach) only for S3 and DDB, and require routing updates; Interface endpoints support more services.
Know the difference between services like Amazon GuardDuty (which detect anomalous behaviour and threats) and Amazon Inspector (which is for vulnerability management).
Any mention of PII usually means Amazon Macie.
Encrypting data is a key strategy to prevent the accidental leakage of data. By controlling access to the decryption keys, you give yourself another layer of control to prevent unintended exposure of sensitive data, regardless of the services being used.
Security Hub aggregates the result from other services (such as Config, Inspector, WAF, Macie, etc) to generate its reports and alerts, so make sure they're available.
AWS Service Catalogue featured in multiple questions where it was used to limit deployments to approved resources and configurations.
When quarantining a compromised instance, pay attention to the uptime requirements. You can quarantine by changing its security groups, or by moving the instance in to an isolated subnet; but changing an instance's subnet will require you to take it offline, but changing its SG won't.
Knowing how to set up a SAML identity provider in IAM helped on a few different questions about federation and SAML metadata changes.
Don't forget that AWS Certificate Manager certifications for CloudFront need to be provisioned in the us-east-1 (N. Virginia) region.
There were quite a few questions including CloudWatch Log. Keep in mind that CW Logs's IAM actions are in the logs: namespace, not cloudwatch:, and log deliverability is usually handled by the SSM agent.
Amazon Identity Center has a built-in user directory that can be used as an IdP for AWS-only solutions.
Know the difference between VPC NACLs (stateless, coarse) and Security Groups (stateful, fine-grained), as well as their defaults, features, and limitations. By default, Security Groups will allow all outbound traffic, and no inbound traffic.
Both S3 lifecycle configuration and DynamoDB item TTL provide a way to expire data for security reasons, limiting the potential for unintended exposure.
AWS Audit Manager featured in multiple questions; keep in mind it can work with on-premises resources for hybrid reports.
Know the various ways for delivering notifications: Amazon SNS can be used for low-cost email notifications (aka. "cost-effective"), Amazon SES (preferred for scale and deliverability), and Amazon SQS (used for messaging, but not email!)
Surprises
Fortunately, there were only a few surprises for me on this exam:
- I had a question about DNSSEC for Route53 which caught me unawares.
- X-Frame-Options headers can be added to origin response policies in CloudFront distributions.
- Somehow I'd managed to skip AWS Signer in my review, but it only featured lightly and unlike a lot of other AWS services, the name actually tells you what it does (code signing for containers and functions) 🙃
- I haven't had a chance to use Glacier Vaults, so I wasn't sure if or when you could change them; it turns out you have a 24-hour window to abort the lock and update the policy before it become immutable.
There were also a few omissions that surprised me, but this could have just been luck of the draw:
- I didn't get any questions about session policies.
- I only saw AWS CodeArtifact in distractor responses.
Having seen the exam evolve and change over time, I think this new version of the certification is an improvement over previous iterations, and would recommended it to people working with AWS seriously or on a daily basis - it's hard to overstate the importance of security in the cloud!
Being able to build secure applications on AWS, or assess an existing solution for potential security issues or improvements is a valuable skill, and one that I think will only become more important in the future. I think this exam is a good measure of someone's understanding of the security offerings and features on AWS.